Gozi Banking Malware Returns, Backed By ‘Dark Cloud’ Botnet

The infamous Gozi banking Trojan is being used in targeted attacks deployed over surprisingly sophisticated botnet infrastructure, finds Cisco
Cisco researchers have warned of new targeted attacks that are seeing the well-known Gozi banking malware deployed over an advanced botnet.
Gozi first came to prominence in January of 2013, when a global sting involving British police and the FBI saw three men charged in operating the malware.
At the time it was believed to have infected at least one million systems and to have resulted in the theft of tens of millions of dollars pilfered from US banks. The crime spree was considered the biggest organised banking malware operation to date.
Gozi uses spyware techniques to steal bank login details.

New attacks
The most recent attacks, monitored over the past six months by Cisco’s Talos security group, involve smaller numbers of strikes targeting specific organisations.
“They do not appear to send large amounts of spam messages to the organisations being targeted, instead choosing to stay under the radar while putting extra effort into the creation of convincing emails,” wrote Talos’ Holger Unterbrink in an advisory.
What’s more, Cisco found Gozi is now being deployed and controlled using an advanced botnet known as ‘Dark Cloud’.
Like other botnets, Dark Cloud operates on legitimate systems that have been infected with malware.
Cybercrime ‘laundry list’
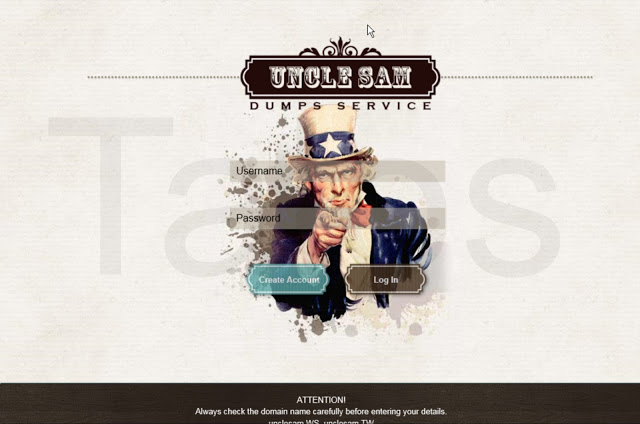
Cisco Talos said they observed the infrastructure being used to carry out “a laundry list of cybercriminal activities”, including distributing services related to payment card crime.
What makes Dark Cloud unusual is its use of advanced techniques to conceal the location of its back-end systems, making it more difficult for those machines to be tracked down and disabled.
The botnet employs ‘fast flux’ techniques, which involves frequent changes to the DNS records associated with malicious domains. One card fraud forum called Uncle Sam was found to use 287 unique IP addresses over a 24-hour period, rotating the addresses roughly every five minutes.
“This demonstrates just how fluid the DNS configuration associated with these domains is and how much infrastructure is being used by these attackers,” Unterbrink wrote.
The criminals behind the latest Gozi attacks are using similar techniques, rapidly changing their distribution and command infrastructure.
Evading detection
“The attackers appear to be very quickly moving to new domains and IP addresses, not only for each campaign, but also for individual emails that are part of the same campaign,” wrote Unterbrink.
He said Talos analysed campaigns that took place during the fourth quarter of last year and have continued into 2018, with new campaigns being launched every week.
Gozi is using other methods to evade security software as well.
For instance, Talos found the infected documents that launch the malware wait until the user closes the document to launch an embedded malicious macro.
“Executing the macro when the document is closed is a clever trick to bypass some sandbox systems, which only open the documents, but never close them during analysis,” wrote Unterbrink.
He said organisations can protect themselves with antivirus software.
Do you know all about biometrics and security? Try our quiz!