Engineers Develop Algorithm To Slow Incoming Cyber Attacks
Engineers claim to have invented an algorithm that will give system administrators vital breathing space during a cyber attack
Security engineers claimed to have invented an algorithm that will slow down incoming cyber attacks and give system administrators time to shore up their defences.
The claim was made by engineers at the University of Tulsa, who said their algorithm can detect incoming cyber attacks against critical infrastructure, such as power grids, in real-time.
Bullet time
Essentially, the way this algorithm works is to slow down internet traffic, including malicious data, in order to give networks time to deal with attacks.
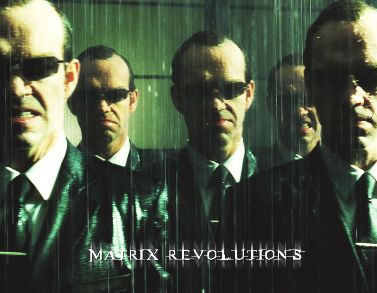
 According to the New Scientist, the engineers were inspired by the Matrix film trilogy and its bullet time sequence, where the hero character Neo is able to slow down time and move out of the path of incoming bullets.
According to the New Scientist, the engineers were inspired by the Matrix film trilogy and its bullet time sequence, where the hero character Neo is able to slow down time and move out of the path of incoming bullets.
When the algorithm senses a cyber attack, it sends “hyper-speed signals accelerating ahead of the malicious data packets to mobilise defences.”
“Slowing the malicious traffic by just a few milliseconds will let the hyper-speed commands activate sophisticated network-defence mechanisms,” a Tulsa engineer Dr Sujeet Shenoi was quoted as saying.
The team explained their concept in a paper published in the International Journal of Critical Infrastructure Protection.
“Hyperspeed signalling uses optimal paths to transmit high priority traffic while other traffic is sent along suboptimal (slower) paths. Slowing the traffic ever so slightly enables the faster command and control messages to implement sophisticated network defence mechanisms,” the paper’s abstract read.
“The core defensive capabilities offered by hyperspeed signaling include distributed filtering, teleporting packets, quarantining network devices, tagging and tracking suspicious packets, projecting holographic network topologies and transfiguring networks.”
However, it remains to be seen whether this development could be used in commercial environments. Shenoi admitted “it would not be cheap to convert an existing network into one that can run the Tulsa team’s algorithm”.
Self monitoring
However, another group of researchers have reportedly developed software that can effectively monitor itself. According to the New Scientist, this software is being developed by a team led by Jason (not Keanu) Reeves at Dartmouth College in Hanover, New Hampshire.
The software works by monitoring the kernel – the bit of code that mediates between the software on one side and the processor and memory on the other.
“We detect changes in the sequence of code the program runs, ones often introduced by malicious programs. We can also verify the operating system code to see if it has been modified by malware,” Reeves was quoted as saying.
It is feasible that this system, which is set up for power-grid-embedded computers running Linux, could be used to trigger the Tulsa algorithm, Reeves added.
“Our system detects the presence of untrustworthy behaviour and leaves the response up to the administrator,” said Reeves.
Not quite what his namesake Keanu does in the Matrix films, but you get the picture.
Think you know security? Test yourself with our quiz!