DefCon: Hackers Find Voting Machine Security Flaws
Five voting machines, most of which are currently in use in the US, were found to be easily hackable at the first event of its kind
Dozens of machines of the kind used in the US voting system were easily hacked in the first event of its kind at the annual DefCon security conference held in Las Vegas over the weekend, adding to long-standing concerns about the security of such devices.
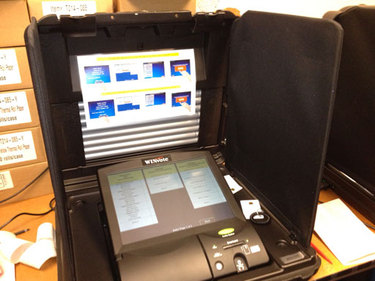
The event presented a “hacker voting village” with about 30 voting machines set up for attendees to try their skills on. All but one are still actively used in elections, and the decommissionned model, Advanced Voting Solutions’ (AVS) WinVote system, was only taken out of service in 2015, organisers said.
Vulnerabilities
Attendees were able to break into the AVS machine and four others, including a Diebold system, according to a report on Sunday by USA Today.
Carsten Schurman, a computer science professor at the University of Copenhagen in Denmark, said he was able to access the AVS machine over a laptop Wi-Fi connection and break into it using a 2003 Windows XP exploit that AVS never patched.
![]()
San Francisco security firm Synack said it took a different approach, plugging in a mouse and keyboard into two freely accessible USB ports on the back of the WinVote system. They then pressed control-alt-delete, entered a default administrator password found on the internet (which can’t be changed) and gained access to the underlying Windows XP software.
Synack intern Anne-Marie Hwang demonstrated how to change the vote tally stored on the machine, a matter of altering an Office file and placing it back on the system, according to CNET.
Vote alteration
Another attendee installed Windows Media Player on the WinVote and played Rick Astley’s 1987 single “Never Gonna Give You Up”.
Synack and Schurman both said they installed software that in theory would allow them to access the machine remotely, but such systems generally aren’t connected to the Internet.
In general, the decentralised nature of the voting system means it would be difficult to tamper with it on a significant scale, FBI director James Comey argued before the 2016 presidential elections.
Critics of the use of digital voting machines have long warned that they’re susceptible to hacking, but until recently researchers faced jail time under the US’ Digital Millennium Copyright Act (DMCA) if they tried to hack the machines for security purposes.
![]() An exception added by the Library of Congress in 2015 now allows hackers to test the machines, but not to discuss their findings to a level of detail that would allow others to use the same tactics.
An exception added by the Library of Congress in 2015 now allows hackers to test the machines, but not to discuss their findings to a level of detail that would allow others to use the same tactics.
The WinVote system is an exception since it’s no longer in use, and AVS went out of business in 2007.
Paper ballots?
But the system, nicknamed “America’s worst voting machine”, was used in three presidential elections, those of 2004, 2008 and 2012.
DefCon’s organisers said attendees were able to discover and exploit previously unknown vulnerabilities on five different models of voting machines.
Vote tampering became a hot issue after allegations of Russian interference with last year’s presidential elections. US officials say there’s no evidence any votes were altered.
But Jake Braun, a former Department of Homeland Security advisor and one of DefCon’s organisers, said the event shows tampering is possible.
“The security is so lax and so bad that they have no way of going back and doing the forensics and saying one way or the other,” Braun told Politico.
Advocacy group Verified Voting said it is pushing for the required use of paper ballots and mandatory auditing computers ahead of the 2018 US midterm elections and 2020 presidential elections.
Other hacking areas at DefCon included automobiles, encryption, lock picking, social engineering and healthcare.
Do you know all about security in 2017? Try our quiz!