Botnet Launches DDoS Attacks From Thousands Of Android Devices

The WireX botnet used hundreds of infected Android apps on Google Play and elsewhere to launch attack traffic against content providers
Researchers have identified a botnet that ran on more than 100,000 Android devices and used their internet connections to launch distributed denial-of-service (DDoS) attacks in one of the first times Google’s mobile platform has been targeted by a botnet.
The WireX botnet was discovered when a number of online content providers and content delivery networks were hit by DDoS attacks on 17 August. Researchers tracked the attacks to hundreds of malicious applications that had been downloaded from Google Play and elsewhere.
Botnet takedown
Google said it removed about 300 apps from its Play Store alone and researchers said the company’s PlayProtect no longer allows the apps involved to install.
The search giant said it’s also in the process of removing the malware from all Android devices.
The malware was also found in other well-known, preconfigured mobile app stores, researchers said.
The incident is the latest in which internet-connected devices have been used to launch attacks. Last year the Mirai botnet, which infects Linux-based devices such as IP cameras and home routers, was used to carry out high-profile attacks on French hosting company OVH and DNS services provider Dyn, and has been used to carry out more attacks this year.
In this case the botnet was identified before it had developed the ability to carry out large-scale attacks, according to researchers. They observed WireX making use of more than 120,000 IP addresses and directing up to 20,000 HTTP requests per second at targets, which they called “significant”, but which is still relatively manageable.
Innocuous apps
DDoS attacks attempt to overwhelm server resources so that a site or resource becomes unavailable to legitimate users. Dismantling the botnets that drive such attacks can be complex due to the complexity of identifying the systems that are involved, generally without the knowledge of their legitimate users.
WireX used systems spread across more than 100 countries, which is unusual for current botnets, researchers said.
A number of companies collaborated to identify the source of the attacks, including Akamai, Cloudflare, Flashpoint, Google, Oracle Dyn, RiskIQ, Team Cymru and others.
They determined that WireX devices presented a user agent identifier made up of the 26 letters of the English alphabet in a random order, and by searching through logs from previous incidents they determined the botnet had been used in smaller attacks as far back as 2 August. As of 15 August the botnet carried out attacks involving at least 70,000 IP addresses, researchers said.
![]()
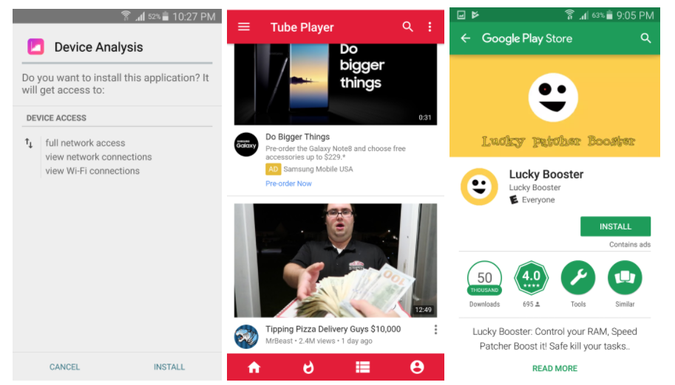
WireX apps present themselves as software such as media or video players, ringtone modifiers or storage managers and launch a service in the background that polls a remote server for attack commands and generates out DDoS traffic. The malware uses what may be a click-fraud engine repurposed for DDoS.
Collaboration key
In one case the app involved was a bare-bones ringtone software presenting only three tones. Researchers found the DDoS engine continued to carry out attacks even when the phone’s screen was locked.
“When we left the phone on a charger and let it go to sleep, it continued to launch DDoS attacks,” they wrote in an advisory simultaneously published by Akamai, Cloudflare, Flashpoint, and RiskIQ.
The researchers emphasised the importance of collaboration to identifying WireX and urged organisations to share metrics related to attacks to help identify future malware.
“These metrics include packet captures, lists of attacking IP addresses, ransom notes, request headers, and any patterns of interest,” they wrote.
Do you know all about security in 2017? Try our quiz!