Avast CCleaner Utility ‘Installed Malware’ For One Month

The popular utility CCleaner was apparently accessed by hackers and made to distribute malware during the month to mid-September, researchers say
A popular PC maintenance application distributed malicious code for a period of nearly one month after hackers apparently accessed the company’s servers, according to both the firm and independent security researchers.
London-based Piriform said on Monday it discovered the malware last week, on Tuesday, 12 September and immediately removed the affected programs.
Malware distribution
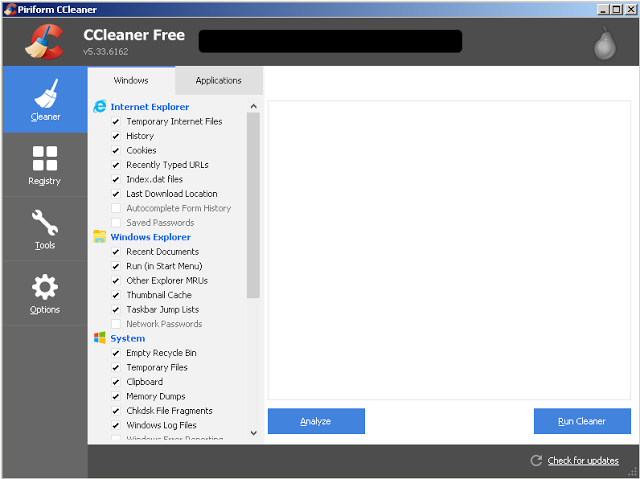
The malware was being installed by version 5.33.6162 of CCleaner, a utility for speeding up PCs and Android devices, and version 1.07.3191 of CCleaner Cloud, according to Piriform.
Cisco’s Talos security group said the affected version of CCleaner was available on Piriform’s website from 15 August to 12 September, or nearly one month. It noted that Piriform claims CCleaner was downloaded more than 2 billion times as of November 2016, with 5 million new users a week.
“The impact of this attack could be severe given the extremely high number of systems possibly affected,” Cisco said in a Monday advisory.
Prague-based computer security firm Avast, which acquired Piriform in July, estimated 2.27 million users had downloaded the infected software.
But Piriform said the issue appeared to have been neutralised before customers were affected.
The affected version of CCleaner included code that installed malware capable of downloading and executing malicious programs on the affected system. But Piriform said the hackers’ control server had been disabled and the alternative servers used by the malware weren’t accessible, meaning there was no way for hackers to communicate with the malware.
Threat ‘disarmed’
“To the best of our knowledge, we were able to disarm the threat before it was able to do any harm,” said Piriform vice president of products Paul Yung in a blog post.
He said users of CCleaner Cloud were being automatically updated to the latest version as a precaution. The basic version of CCleaner doesn’t include an automatic update feature, so Yung urged users to update.
However, Cisco noted that updating the software doesn’t remove the malware from the systems of affected users.
“Affected systems need to be restored to a state before 15 August, 2017 or reinstalled,” Cisco stated.
Piriform’s Yung said only Windows users appeared to have been affected, but he didn’t estimate how many had downloaded the infected installers.
![]() Cisco said its records showed hundreds or thousands of systems attempting to access the control servers specified by the malware during the period it was being installed by CCleaner.
Cisco said its records showed hundreds or thousands of systems attempting to access the control servers specified by the malware during the period it was being installed by CCleaner.
Installer used valid certificate
Cisco noted that the malware was installed by an authentic version of CCleaner signed using a valid security certificate, suggesting an attacker may have compromised Piriform’s development or build environment. The malware could also have been inserted by an insider, Cisco suggested.
Yung declined to speculate on how the code appeared in CCleaner or where the attack originated from.
“The investigation is still ongoing,” he wrote.
Cisco said the attack, which recalls the methods used to spread the damaging ‘NotPetya’ malware in June, indicated the increasingly complex techniques in use by attackers.
“Data received from… software vendors rarely receives the same level of scrutiny as that which is applied to what is perceived as untrusted sources,” Cisco wrote. “Attackers have shown that they are willing to leverage this trust to distribute malware while remaining undetected.”
Do you know all about security in 2017? Try our quiz!