NHS Lanarkshire Blames Missing Patch For WannaCry Impact

Oops. Health board in Scotland admits WannaCry ransomware attack was down to vital patch not being rolled out
One of Scotland’s largest health boards failed to ensure that its IT systems were fully patched with a vital security update, which left it vulnerable to a widespread cyber attack.
NHS Lanarkshire had been one worst-hit health authorities in Scotland when the WannaCry ransomware wrecked havoc across the UK (and indeed the world) starting on May 12.
Eleven of Scotland’s 14 territorial health boards had been affected in that attack, and it forced NHS Lanarkshire (NHSL) to cancel 494 patient appointments and procedures at that time. But no data was lost or was unrecoverable.
WannaCry Attack
And then in August NHS Lanarkshire confirmed that its IT systems and network had been infected again by a new variant of the Bitpaymer malware.
That ransomware attack in August led to 184 operations and doctors’ appointments being cancelled.
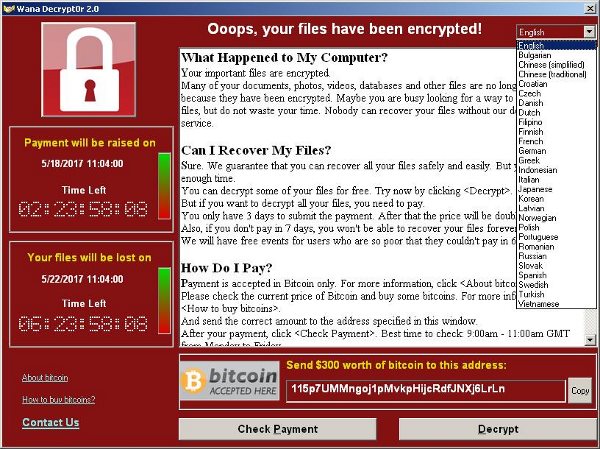
Ransomware encrypts data on the systems of those attacked and demands a payment to unlock the files. The WannaCry ransomware hit 150 countries in May, and typically demanded $300 (£230) in bitcoins to restore infected computers.
NHS Lanarkshire is Scotland’s third-largest health board and serves more than 650,000 people.
And now it has admitted in a ‘Significant Adverse Event Review Report‘ on the WannaCry attack, that its patching process had left it vulnerable, along with a couple of other issues.
This is despite the report stating that NHSL had recognised the increasing risk from cyber-attack back in 2015.
“While the malware affected many NHS organisations across England and Scotland, it had a significant impact on NHSL, with 1338 PCs affected in both acute and primary care settings,” the report said of the WannaCry attack in May.
“Over the course of the week following the incident, the infected PCs were either cleansed of virus on site or were replaced while cleansing took place. This was done on a prioritised basis, with additional IT support being provided by NHS Greater Glasgow and Clyde and NHS Ayrshire and Arran.”
What Went Wrong
The report found three main technical issues had led to NHS Lanarkshire being affected by WannaCry.
The first that while Microsoft had actually released a security patch in March 2017 that blocked WannaCry, it had only been deployed on GP servers, but “had not been rolled out due to ongoing testing and limited resources to deploy the patch sooner.”
The second issue was that unbelievably NHSL was still using 395 PCs that ran Windows XP – support for which had ended back in 2014.
Microsoft subsequently made a WannaCry patch available for XP systems.
NHSL said that a previous audit had incorrectly found there were no XP-running PCs, but in reality 190 of these PCs were still required to run XP as they were supporting medical devices which could not operate on more up to date software.
The third issue was that a configuration on desktop PCs called SMB version 1 was left on. The SMB configuration needed to be active in order for the Board’s laboratory system to operate effectively. The active SMB configuration was exploited by the malware to allow it to move across internal networks, said the report.
“As a result of these findings, the review team has concluded that there were major service issues that contributed to the event,” the report stated. “There were no significant adverse patient outcomes although there was the potential for major service implications.”
Do you know all about security in 2017? Try our quiz!