Cisco, Samsung, Intel And Others Targeted By CCleaner Hidden Malware
The supply chain attack was sophisticated and could have been state-sponsored
Malware hidden behind Avast’s CCleaner software has been designed to attack technology giants such as Cisco, Samsung, Intel, VMware and Google, according to further research by Cisco’s Talos security team.
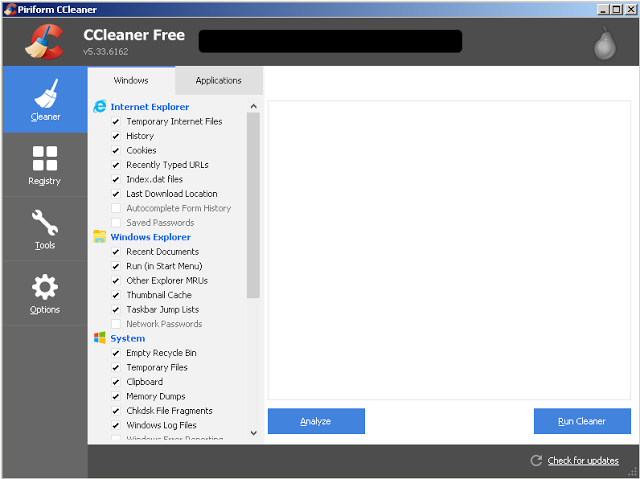
Having first spotted that two versions of CCleaner, version 5.33.6162 and version 1.07.3191 of CCleaner Cloud, had malware secretly loaded onto them from a hijacked server, the Talos team has been continuing its research into the software supply chain attack, despite Avast playing down the cyber security risk.
From analysing archived files, the Talos researchers found that specific companies were targeted by the malware lurking in CCleaner with the domain names of targeted companies in the delivery code the malware’s command and control server was using.
“During our investigation we were provided an archive containing files that were stored on the C2 server. Initially, we had concerns about the legitimacy of the files. However, we were able to quickly verify that the files were very likely genuine based upon the web server configuration files and the fact that our research activity was reflected in the contents of the MySQL database included in the archived files,” the Talos researchers explained.
“In analysing the delivery code from the C2 server, what immediately stands out is a list of organisations, including Cisco, that were specifically targeted through delivery of a second-stage loader. Based on a review of the C2 tracking database, which only covers four days in September, we can confirm that at least 20 victim machines were served specialised secondary payloads.”
Hidden hackers
![]() While Avast has moved to kick the hackers off the hijacked server and roll out an updated version of CCleaner purged from malware, the Talos team noted that their discovery of the targeted malware was concerning as it would point to the hacker or hackers having access to sophisticated cyber attack techniques and malware.
While Avast has moved to kick the hackers off the hijacked server and roll out an updated version of CCleaner purged from malware, the Talos team noted that their discovery of the targeted malware was concerning as it would point to the hacker or hackers having access to sophisticated cyber attack techniques and malware.
“These findings also support and reinforce our previous recommendation that those impacted by this supply chain attack should not simply remove the affected version of CCleaner or update to the latest version, but should restore from backups or reimage systems to ensure that they completely remove not only the backdoored version of CCleaner but also any other malware that may be resident on the system,” they advised.
Avast is currently trying to find the source of the attack, and given the malware lurking behind CCleaner managed to infect more than two million users but only seemed interested in servers and domains belonging to a handful of companies, there is a chance that the perpetrators were state-sponsored.
“We are not excluding any possibility. It is possible that this was the result of a State level attack or industrial espionage,” an Avast spokeswoman told TechCrunch.
“However, rather than speculate, we are focused on working with law enforcement to identify the perpetrators and prevent any damage caused by a second stage payload.”
With cyber attacks getting more sophisticated in the vein of the NotPetya attacks, it would not be too surprising if a state-sponsored or powerful hacker group was behind the CCleaner malware infection.
Do you know all about security in 2017? Try our quiz!